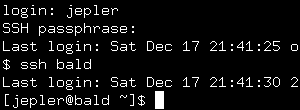
A console login mediated by pam_ssh
The only snag I ran into on FC2 was that the script in /etc/X11/xdm/Xsession unconditionally started a fresh ssh-agent, even if $SSH_AGENT_PID was already set. I changed the SSHAGENT= line to read [ -x /usr/bin/ssh-agent && -z "$SSH_AGENT_PID" ] && SSHAGENT="/usr/bin/ssh-agent" and then everything worked. I'm now using it for console and gdm logins on one of my machines.
On FC2 I built the rpm from the tarball. It looks like FC4 has one available via yum.
Update 2006/01/09: I was having trouble with pam_ssh not leaving an
ssh-agent running the next time I logged in after a crash (dead battery). I
discovered that the problem was that leftover ~/.ssh/agent-* files would
trick pam_ssh into thinking that an appropriate ssh-agent was already running.
I now remove these files in /etc/rc.local when booting.
Entry first conceived on 18 December 2005, 3:49 UTC, last modified on 15 January 2012, 3:46 UTC
Website Copyright © 2004-2024 Jeff Epler